👉Identity theft definition
Identity
theft is the use of someone else's personal information without permission,
typically to conduct financial transactions. By personal information, we mean
data that institutions use to recognize any individual associated with the
institutions. Examples are social security number, bank account number, address
history, and soon and so forth.
These types
of valuable information are in theory private and should be treated as SPII, but
in practice can often be discovered in a variety of ways by a dedicated
identity thief, who can then either access individual’s own accounts or open
new ones in your name. The latter practice can be particularly having a harmful effect, with just your social security number,
identity thieves can take out loans or credit cards that they never pay off —
and the resulting damage to your credit rating can be very difficult to undo.
While identity theft is a very old crime, in many ways it is a defining problem of our modern
digital age, in which your personal information can easily be exposed online
due to your own negligence or the poor security practices of companies you do business
with, and so much of your financial life rides on the accuracy of your credit
rating. The damage can be mitigated, but it's better to prevent the theft in
the first place.
Impact of identity theft on business
Identity
theft is most often associated with the act of stealing an individual's
identity.
Here we
are talking about an identity thief pretending to be someone within a company
who has the authority to make financial transactions, just like they might
pretend to be another individual.
The
consequences can be dire, particularly for small businesses where the founder's
or owner's finances are deeply entangled with the company's.
How is identity theft committed?
·

Many of these techniques would work on both individuals and businesses. Businesses are often less strict about controlling "personally" identifying information than individuals, since certain facts about businesses must be public by law, and a business is run by multiple people and lines of responsibility may be diffuse.
Identity theft examples
Once
identity thieves have identifying information about you or your company,
there's a lot of different techniques they can use to profit from it.
- Accessing existing financial accounts. This is probably the most straightforward way to
profit from identity theft-- by simply stealing your money. With a credit card
or bank account number, identity thieves can make purchases until the fraud is
noticed and the accounts frozen. Businesses, which may have large amounts of
cash or credit for day-to-day operations, are a particularly tempting target.
- Opening a fraudulent credit card or other line of
credit. This can be achieved with as little data as a name
and a social security number. Once the credit is available to the identity
thief, money can be withdrawn and spent or charges made to the card — and of
course they'll make no attempt to pay off the loan. Since the debt is attached
to the victim's social security number, there are little or no consequences for
the identity thief. Again, businesses are a particularly tempting victim of
these scams, as they can often acquire bigger lines of credit than individuals
can.
Identity
theft protection
There's
a wealth of information out there on how to protect yourself from identity
theft, from outlets ranging from credit agencies to government websites to
personal finance publications. While the details differ, there are some bits of
advice that almost everyone seems to agree on, and they apply to individuals
and businesses alike.
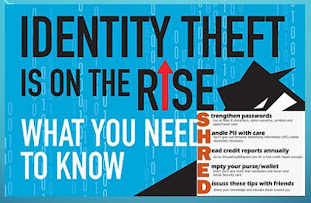
Following
are the points we can practice to our confidential data safe from theft.
1.
Don't share personal
information (birthdate, Social Security number, or bank account number) because
someone asks for it.
2.
Pay attention to
your billing cycles. If bills or
financial statements are late, contact the sender.
3. Secure your Social
Security number (SSN). Don't carry your Social Security card in your wallet.
Only give out your SSN when necessary.
4.
Collect mail every day. Place
a hold on your mail when you are away from home for several days.
5. Store personal information in a safe place.
6. Install firewalls and virus-detection software on your home computer.
7. Create complex passwords that
identity thieves cannot guess. Change your passwords if a company that you do
business with has a breach of its databases
8. Update sharing and firewall settings when you're on a public wi-fi network. Use a virtual private network (VPN), if you use
public wi-fi.
How to report identity theft
That's
a long list of precautions you need to take, and while many people make strong
efforts to meet all of them, it's hard to do it all perfectly — and an identity
thief only needs to get lucky once. And as we've noted, many identity thieves
get personal data derived from hacks of corporate systems, so even if you've
been completely vigilant about your data, you can still find yourself a victim
of identity theft if some company you've done business with lets down its
guard.
If you think,
you have been hacked or your confidential information are compromised, here are
few tips you can follow.
1. Pull your credit report. Every year, you’re entitled to one free credit report
from each of the main credit card company You can access these reports from the
respective credit card issuer company’s website as well.
2. File a police report and fraud affidavit. These can be obtained from your creditor(s) recovery department,
and provide copies of these documents and any additional necessary paperwork to
creditors’ fraud departments.
3. Create an Identity Theft Report. Do inform the credit card issuer about the fraud
online .The online report asks a few questions about your situation, then
devises a personal recovery plan.
4. Place an extended fraud alert on your credit file. This alert lasts seven years and is available only to
identity theft victims. To get an extended fraud alert, you’ll first need to
fill out an Identity Theft Report.
5.
Make a list of suspicious activity. Applications
to open new accounts, as well as the accounts that have already been
fraudulently opened in your name, must be noted and forwarded to the three
credit bureaus and listed on your Identity Theft Report.
6.
Provide
creditors’ fraud departments with the details and contacts. It will take up to 90 days to conduct a full
investigation.
7. Obtain letters from your creditors. These letters should state that the fraudulence
on your account has been confirmed, resolved and removed from your account.
Then make sure that your creditors have expunged this negative reporting on
your account and that a letter stating this has been sent to all three credit
reporting bureaus. (As a backup, you should personally send a copy of these
letters to the credit reporting agencies as well.) Be sure to call afterward to
make sure that they have received this information.
Conclusion
Identity
theft not only impacts you financially but emotionally as well. The emotional
stress can disrupt your sleeping and eating and lead to depression. If such
things happens then giving yourself room to breathe and allowing some time to
pass to repair the damage, noting that recovering from identity theft can be a
process that takes weeks or even months.
 |
| Identity Guard |






1 Comments
Today scenario personal info protection is a challenge. For more on this visithttps://www.theblog-insider.com/2020/05/data-protection.html?m=1