What is an assessment of security risks?
The process of identifying and evaluating risks for assets that could be affected by cyberattacks is known as cybersecurity risk assessment. In essence, you identify threats from both within and without; examine how they might affect things like the integrity, confidentiality, and availability of data; and figure out how much it would cost to suffer a cybersecurity incident. Using this data, you can fine-tune your cybersecurity and data protection measures to your company's actual risk tolerance.
You must respond to three crucial
questions in order to begin an IT security risk assessment:
1. What are
the data that, in the event of loss or exposure, would have a significant
impact on your company's operations? These are your organization's critical
information technology assets.
2. What
essential business procedures call for or make use of this data?
3. What
threats might make it harder for those business functions to function?
You are able to begin design
strategies once you are aware of what you need to safeguard. But before you
spend a penny or an hour of your time implementing a risk-reduction strategy,
think about the type of risk you're dealing with, how important it is to you,
and whether your approach is the most cost-effective.
The significance of conducting
comprehensive IT security assessments on a regular basis developing a solid
foundation for business success is aided by conducting comprehensive IT
security assessments on a regular basis.
In particular, it gives them the ability
to:
Assess potential security partners, Evaluate
potential security partners, Establish, maintain, and demonstrate compliance
with regulations Accurately forecast future needs.
Explanation of cyber risk (IT risk)
definition
According to the Institute of Risk
Management, a cyber risk is “any risk of financial loss, disruption, or
damage to the reputation of an organization from some sort of failure of its
information technology systems.”
Prevent data breaches, choose
appropriate protocols and controls to mitigate risks.
Cybersecurity risks include:
When taking stock of cyber risks, it
is essential to detail the specific financial damage they could cause to the
organization, such as legal fees, operational downtime and related profit loss,
and lost business due to customer distrust. Hardware damage and subsequent data
loss Malware and viruses Compromised credentials Company website failure.
The four essential components of an IT
risk assessment
In a moment, we'll talk about how to
evaluate each one, but first, a brief definition for each:
Threat: Anything
that has the potential to harm an organization's people or assets is a threat.
Natural disasters, website failures, and corporate espionage are examples.
A vulnerability is any potential flaw
that would permit a threat to cause harm. A vulnerability that can make it
possible for a malware attack to succeed, for instance, is out-of-date antivirus
software. A vulnerability that increases the likelihood of equipment damage and
downtime in the event of a hurricane or flood is a server room in the basement.
Disgruntled employees and outdated hardware are two additional examples of
vulnerabilities. A list of specific, code-based vulnerabilities is kept up to
date in the NIST National Vulnerability Database.
The total damage an organization would
suffer if a vulnerability were exploited by a threat is referred to as the
impact. A successful ransomware attack, for instance, could result in not only
lost productivity and costs associated with data recovery but also the
disclosure of customer data or trade secrets, which could result in lost
business as well as legal costs and penalties for compliance.
Probability — This is
the likelihood that a danger will happen. Usually, it's a range rather than a
single number.
Risk = Threat x Vulnerability x
Asset. The following equation can be used to understand risk: Despite
the fact that risk is represented here as a mathematical formula, it is not
about numbers; It is a well-thought-out plan. Take, for instance, the scenario
in which you want to determine the level of danger posed by the possibility of
a system being hacked. Your risk is high if the asset is crucial and your
network is extremely vulnerable (perhaps due to the absence of an antivirus
solution and firewall). However, even though the asset is still critical, your
risk will be medium if you have strong perimeter defences and a low
vulnerability.
There is more to this than just a
mathematical formula; It is a model for comprehending the connections among the
factors that contribute to determining risk:
Threat is an abbreviation for
"threat frequency," which is the anticipated frequency of an adverse
event. One in one million people will, for instance, be struck by lightning in
any given year.
The term "the likelihood that a weakness
or exposure will be exploited and a threat will succeed against an
organization's defences" is abbreviated as "vulnerability."
What is the organization's security
environment like? If a breach does occur, how quickly can it be mitigated to
avoid disaster? How likely is it that any given employee will pose an internal
threat to security control, and how many of them are there?
A security incident's total financial
impact is measured by its cost. Hard costs like hardware damage and soft costs
like lost business and consumer confidence are included. Other expenses
include:
Data loss: The
theft of trade secrets could result in your competitors taking your business.
Loss of trust and customer attrition could result from the theft of customer
information.
System or application downtime:
Customers may be unable to place orders, employees may be unable to perform
their duties or communicate, and so on if a system fails to perform its primary
function.
Legal repercussions: If someone steals
data from one of your databases, even if the data isn't particularly valuable,
you could be hit with fines and other legal fees because you didn't follow
HIPAA, PCI DSS, or other data security regulations.
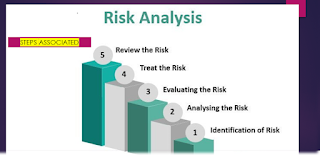
How to conduct a security risk
assessment Now, let's go over how to conduct an IT risk assessment.
1. Identify
and prioritize assets- Servers, client contact information,
confidential documents from partners, trade secrets, and so on are all examples
of assets. Keep in mind that what you consider valuable as a technician
may not actually be the most valuable for the company. As a result, you
must collaborate with management and business users to compile a list of all
valuable assets. Collect, if necessary, the following data for each asset:
- · Software
- · Hardware
- · Data
- · Interfaces
- · Users
- ·
Support Personnel
- ·
Mission or Purpose
- ·
Criticality
- ·
Functional requirements
- ·
IT security policies
- · IT security architecture
- · Network topology
- ·
Information storage protection
- ·
Information flow
- ·
Technical security controls
- ·
Physical security environment
- ·
Environmental security
Since most businesses only have a
small budget for risk assessment, you will probably only need to cover
mission-critical assets for the remaining steps. As a result, you must
establish a standard for assessing each asset's significance. The asset's
monetary value, legal status, and significance to the organization are common
criteria. Use the standard to classify each asset as critical, major, or minor
after it has been approved by management and formally incorporated into the
risk assessment security policy.
2. Identify Threats- Anything that has the potential to harm your business is a threat. While malware and hackers are probably the first to come to mind, there are many other kinds of threats as well.
Natural catastrophes. Fire,
earthquakes, floods, hurricanes, and other natural disasters have the potential
to destroy not only data but also servers and appliances. Consider the
likelihood of various natural disasters when choosing a location for your
servers. For instance, there might be a low chance of tornadoes but a high risk
of flooding in your area.
Absence of hardware. The quality and
age of the server or other machine determine the likelihood of hardware
failure. The likelihood of failure is low for equipment of high quality that is
relatively new. However, the likelihood of failure is significantly increased
if the equipment is old or comes from a "no-name" vendor. No matter
what industry you operate in, you should put this threat on your watch list. It
is possible for people to accidentally delete important files, click on a
malicious link in an email, or spill coffee on critical systems-hosting
equipment.
There are three types of wrongdoing:
When someone damages your business by
physically stealing a computer or server, engineering a distributed denial of
service (DDOS) attack against your website, or deleting data, they are
committing interference.
Your data is stolen through
interception.
Impersonation is the misuse of another
person's credentials, which are typically obtained through social engineering,
brute force, or the dark web.
3. Identify
Vulnerabilities- A weakness that could allow a threat to harm your business is
a vulnerability. Analysis, audit reports, the NIST vulnerability database,
vendor data, information security test and evaluation (ST&E) procedures,
penetration testing, and automated vulnerability scanning tools are all methods
by which vulnerabilities can be identified.
Don't confine your thinking to
software flaws; Additionally, there are human and physical vulnerabilities.
Having your server room in the basement, for instance, increases your
vulnerability to flooding, and not informing employees about the dangers of
clicking on links in emails increases your vulnerability to malware.
4. Controls- To reduce
or eliminate the likelihood that a threat will exploit a vulnerability, analyse
the controls that are either in place or in the planning stage. Encryption,
methods for detecting intrusions, and solutions for identification and
authentication are all examples of technical controls. Security policies,
administrative actions, and physical and environmental mechanisms are examples
of nontechnical controls.
Nontechnical and technical controls
can be further divided into preventive and detective categories. Preventive
controls, as the name suggests, attempt to anticipate and avert attacks;
Devices for authentication and encryption are two examples. Detective controls
are used to find threats that have already happened or are about to happen;
They include intrusion detection systems and audit trails.
5. Determine the Likelihood of an Incident- Consider the type of vulnerability, the capability and motivation of the threat source, and the effectiveness of your controls to determine the likelihood that a vulnerability will actually be exploited. When determining the likelihood of an attack or other adverse event, many organizations use the categories high, medium, and low rather than a numerical score.
The asset's mission and any processes
that are dependent on it; the asset's value to the organization; and the
asset's sensitivity. A business impact analysis (BIA) or mission impact
analysis report can provide this information. The impact of harm to the
organization's information assets, such as loss of confidentiality, integrity,
and availability, is quantified or qualitatively assessed in this document. The
impact on the system can be graded as high, medium, or low qualitatively.
6. Determine the Level of Risk to the IT
System for Each Threat/Vulnerability Pair Prioritize the Information Security
Risks
The risk-level matrix is a useful tool
for estimating risk in this manner. The likelihood that the threat will exploit
the vulnerability. The approximate cost of each of these occurrences. The
suitability of the planned or existing information system security controls for
eliminating or reducing the risk. A probability of 1.0 indicates that the
threat will be met; A value of 0.5 is assigned to a medium likelihood; and a
0.1 rating for a low likelihood of occurrence. In a similar vein, the values
for a high impact level are 100, a medium impact level is 50, and a low impact
level is 10. Risks are categorized as high, medium, or low based on the result
of multiplying the threat likelihood value by the impact value.
7. Recommend Controls - Determine the
necessary steps to reduce the risk using the risk level as a foundation. For
each level of risk, the following are some general guidelines:
High: As soon as possible, a plan for
corrective action should be created.
Medium: Within a reasonable amount of
time, a plan for corrective measures should be developed.
Low: The group must decide whether to
take the risk or do something about it.
Be sure to take into account the
following when evaluating controls to reduce each risk:
Policies of the organization Cost-benefit analysis Operational impact Feasibility Regulatory requirements in effect.
The recommended controls' overall effectiveness, Safety and reliability of the Document ,the Results ,The development of a risk assessment report is the final step in the risk assessment process.
This report will help management make good
decisions about the budget, policies, procedures, and other things. The report
ought to provide a description of the vulnerabilities that correspond to each
threat, the assets that are in danger, the impact on your IT infrastructure,
the likelihood of occurrence, and the control recommendations.
Report on the IT risk assessment- The
risk assessment report can point to important steps that can be taken to reduce
multiple risks. For instance, taking regular backups and storing them off-site
will reduce the likelihood of flooding and accidental file deletion. The
associated costs and business justifications for making the investment should
be explained in detail at each step.
Always keep in mind that the core of
cybersecurity are the enterprise risk management and information security risk
assessment processes. The information security management strategy as a whole
is built on these processes, which answer questions about which threats and vulnerabilities
can cost the company money and how to reduce them.








0 Comments